At home or in the office, ensure that these 9 Top Tips are included on your Cyber Security Checklist.
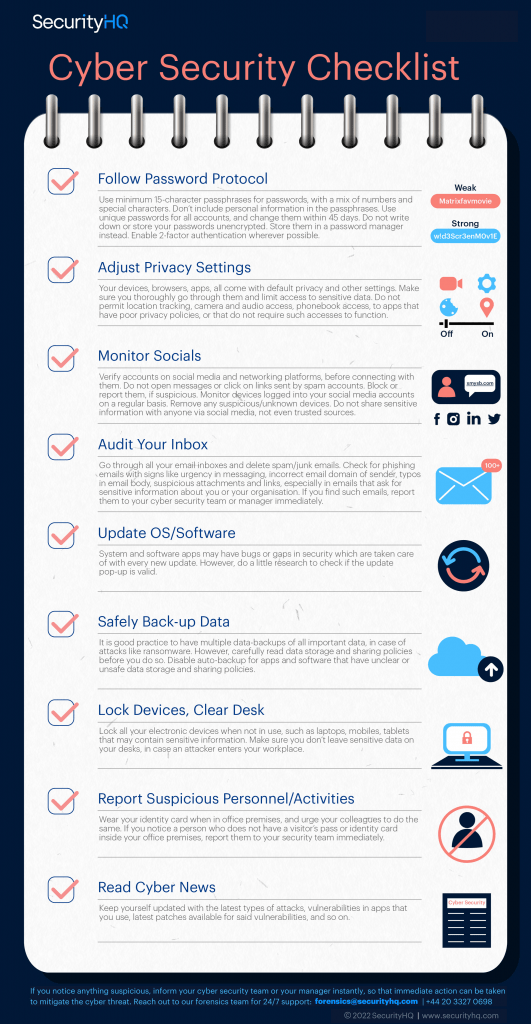
Follow Password Protocol
Use minimum 12-character passphrases for passwords, with a mix of numbers and special characters. Don’t include personal information in the passphrases. Use unique passwords for all your accounts and change them within 45 days. Do not write down or store your passwords unencrypted. Store them in a password manager instead. Enable 2-factor authentication wherever possible.
Adjust Privacy Settings
Your devices, apps, browsers, all come with default privacy and security settings. Make sure you thoroughly go through them and limit access to sensitive data. Do not permit location tracking, camera and audio access, phonebook access to apps that have poor privacy policies, or that do not require such accesses to function.
Monitor Socials
Verify accounts on social media and networking platforms, before connecting with them. Do not open messages or click on links sent by spam accounts. Block or report them, if suspicious. Monitor devices logged into your social media accounts on a regular basis. Remove any suspicious/unknown devices. Do not share sensitive information with anyone via social media, not even trusted connections.
Audit Your Inbox
Go through all your inboxes and delete spam/junk emails. Check for phishing emails with signs of urgency in messaging, incorrect email domain or sender, typos in email body, suspicious attachments and links, especially in emails that ask for sensitive information about you or your organization. If you find such emails, report them to your cyber security team or manager immediately.
Update OS/Software
System and software apps may have bugs or gaps in security which are taken care of with every new update. However, do a little research to check if the update pop-up is valid.
Safely Back-up Data
It is good practice to have multiple data back-ups (physical and cloud based) of all your important data, in case of attacks like ransomware. Before taking this step, carefully read data storage, and sharing policies of the platform. Disable auto back-ups for apps and software that have unclear or unsafe data storage and sharing policies.
Lock Devices, Clear Desks
Lock all your electronic devices that may contain sensitive information, such as laptops, mobiles, tablets, when not in use. Make sure you don’t leaver sensitive data such as passwords, account details, contracts, on your desks in case an attacker enters your workplace.
Report Suspicious Personnel/Activities
Wear your identity card when in office premises and urge your colleagues to do the same. If you notice a person inside your office premises who does not have a visitor’s pass or identity card, report them to your security team immediately.
Read Cyber News
Keep yourself updated with the latest types of attacks, vulnerabilities in apps that you use, latest patches available for said vulnerabilities, and so on.
If you notice anything suspicious, inform your cyber security team or your manager instantly, so that immediate action can be taken to mitigate the cyber threat. Reach out to our forensics team for 24/7 support.
![Cyber Security Checklist [Infographic]](https://www.securityhq.com/wp-content/uploads/2022/09/Cyber-Security-Checklist-Banner-1920-x-928-1.png)
![10 Tips to Protect Your Data [Infographic]](https://www.securityhq.com/wp-content/uploads/2021/07/Thumbnail-image-Tips-to-Protect-Your-Data-blog-copy.jpg)









