Less Panic. More Risk Management
SHQ Response was built so that businesses could learn more about potential threats, and solve cyber related issues, together with their designated security experts.
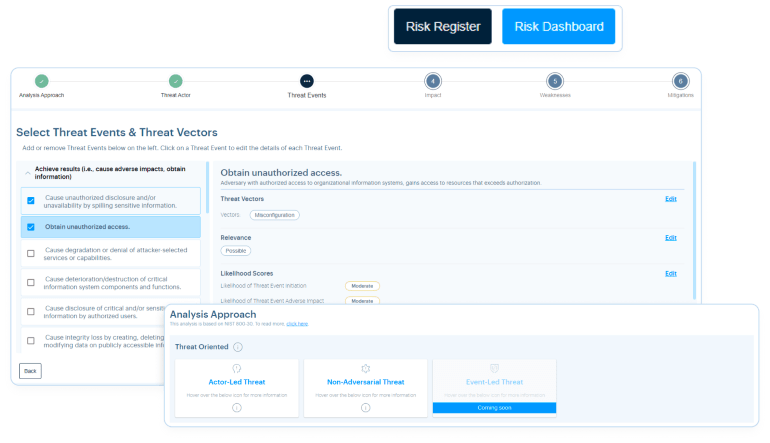
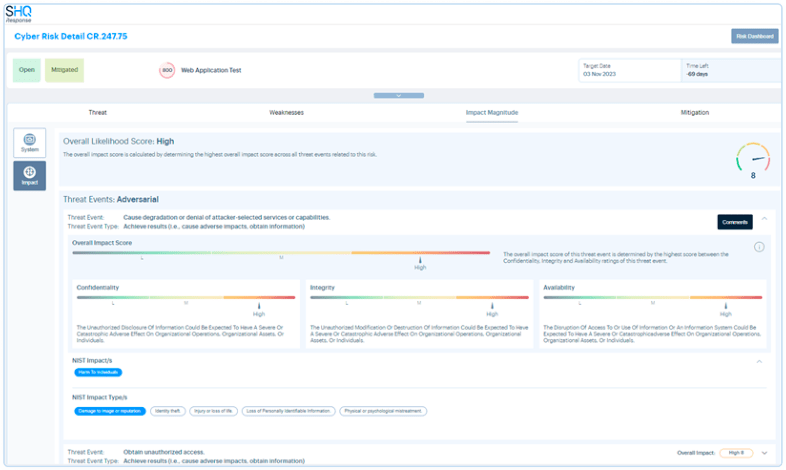
Map Threats, Assets & Vulnerabilities to Derive Risks
Be it 1 or 1000, map all cyber risks targeting your business.
- Map metrics & measurements within cyber security to a custom persona.
- Map and group bad actors, and threat events together.
- Map the total amount of risks to business, in a risk count manner.
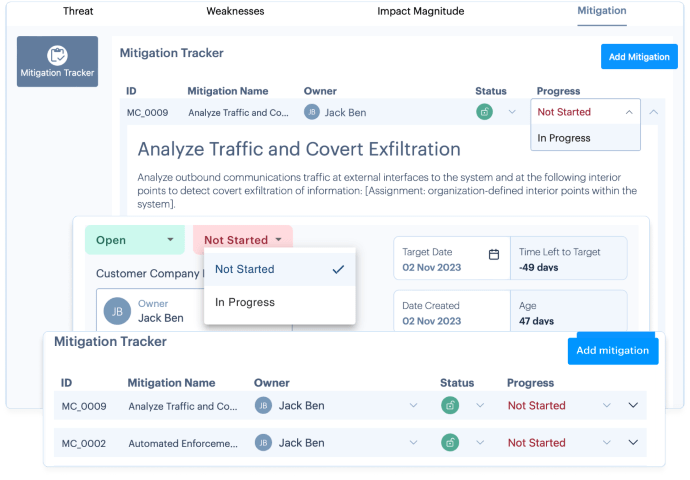
Track Mitigations, Task Assignments, and Progress
Collaborative approach with your SOC Team.
- View all mitigations related to a risk, with the Mitigations tab.
- Receive and assign tasks and mitigations to individuals.
- Select a new progress or status, from anywhere, anytime.
Link Compliance Incidents to Risk
Reduce issues with compliance & uphold the right security policies.
- Enriched & mature compliance processes.
- Ensure currency of knowledge in a changing technical environment.
- Safeguard against hefty fines and maintain brand value.
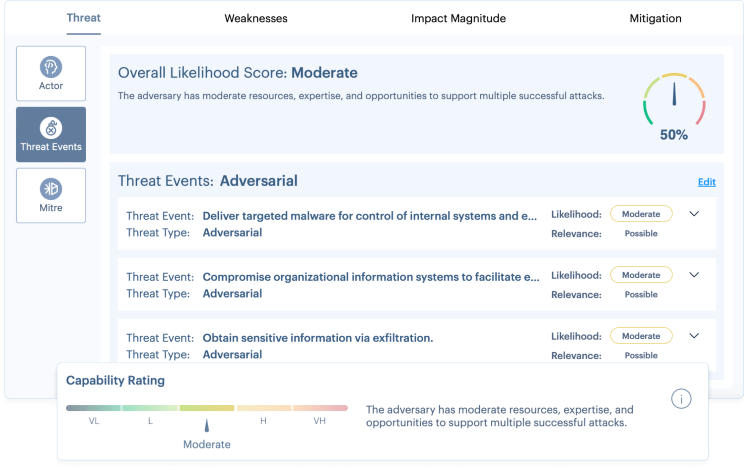
Avoid Emergencies and Pre-empt Threats before they arise
Take actions that make a difference.
- Expert analysts prioritise actions for greatest impact.
- Improve overall response time to risks.
- Impact overall health score of the company.
Monitor, Respond and Recover 24x7
A Unified Security Management Platform



Learn more about SHQ Response
Real Time Dashboard
Data representation in real-time to understand and provide the actual status and actions required.
Automate Containment
Accelerate response to threat containment by automated response to block communications and isolate infected machines.
Collaborative Incident Notification
Notifications with analysis, recommendations, timeline analysis, and activity tracking.
SHQ Response Mobile App
- Quick Collaboration with SOC Analysts.
- Search and Create Tickets.
- Prioritise and Escalate Incidents.
Interactive Visualisations
Data driven interactive visuals to inspect and represent data that identifies risks & problems.
Framework Mapping
Actions mapped to NIST, NCSC, and MITRE, to provide actions on how to deal with risks, how to identify them, and how to raise them.
Request A Demo Today
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.