New and Improved Incident Management & Analytics Platform
Version Update [Version 5.3]
Fully Integrated, Fourth Generation, Incident Management and Analytics Platform.
SecurityHQ are delighted to release our new and improved version of our leading Incident Management and Analytics platform.
What is New?
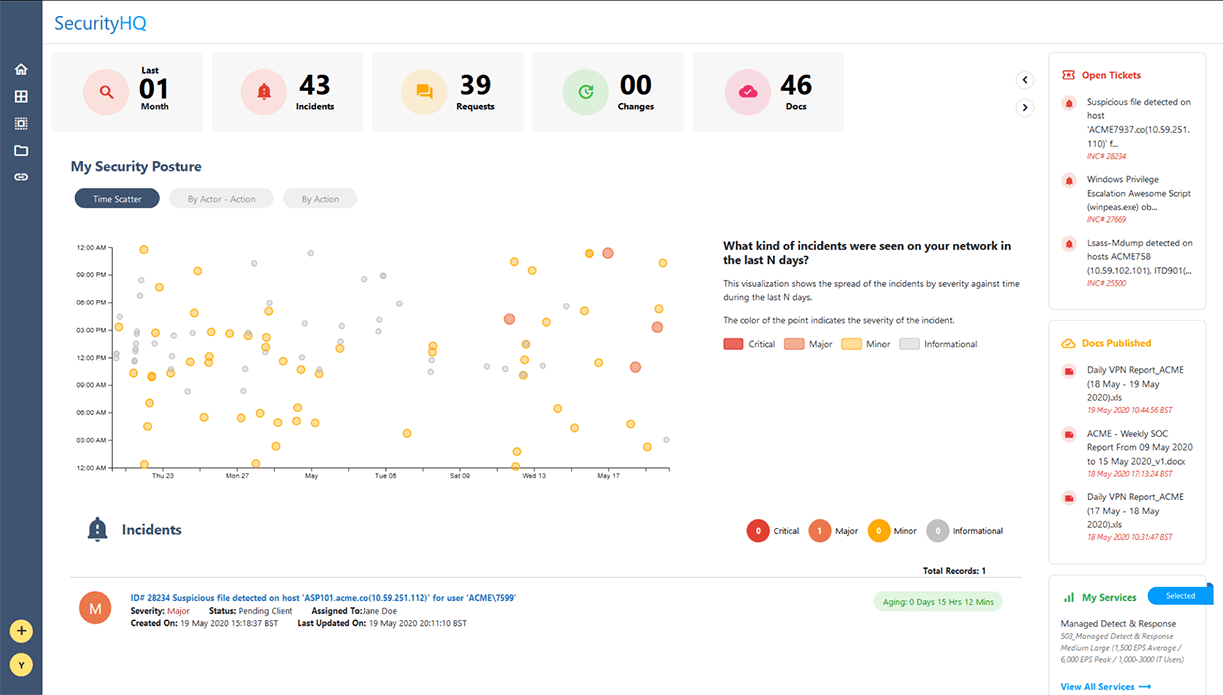
Data-Driven Document Visualisation
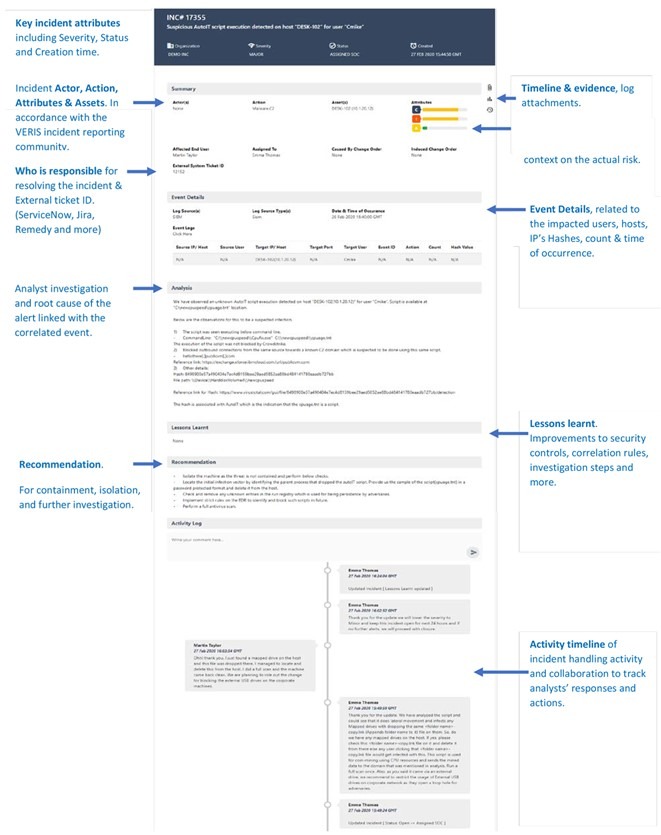
The new Incident Management interface has been designed with the objective to introduce modern standards around data-driven documentation, so that SecurityHQ can present information quickly and intuitively. To do this, visuals need to be interactive. That way, by inspecting data visually through a time series graph or sunburst chart, for instance, you can drill down into the data to identify an accident, its trends, and how this information relates to other artefacts.

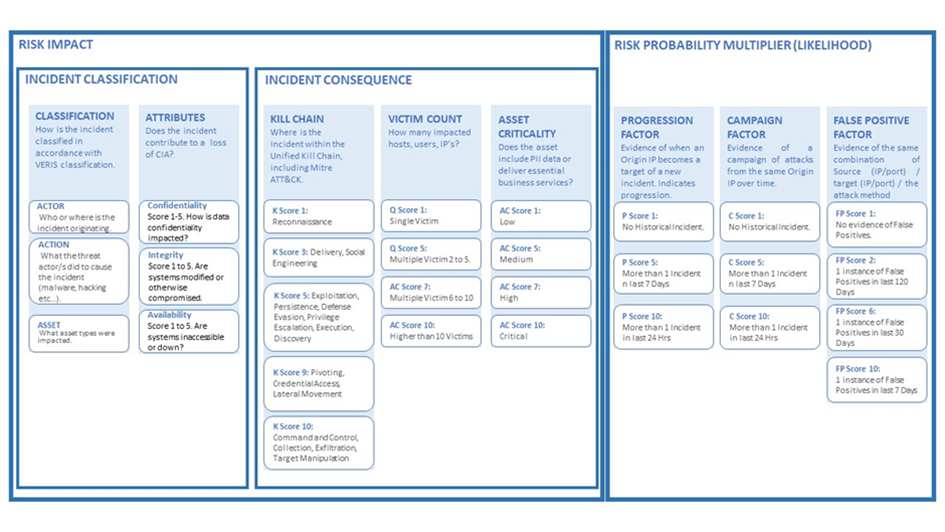
Industry Best Practices Framework
In addition to the new visualisations, SecurityHQ have created a new framework for our incident classification scheme. We believe that an incident classification scheme must have a common taxonomy for how incidents are referenced against industry best practices. There are two best practices that we are using in this case.
The first is VERIS, which is a standard classification for incidents. The second is the MITRE ATT&CK. Both of which are crucial. By dynamically categorising incidents against MITRE ATT&ACK, we can assign the risk of incidents, based on the CIA attributes, asset criticality and the normal behaviour of the impacted assets.
Through this, a common risk rating for an incident is provided, which is based around the CIA value, confidentiality, integrity and availability impact of an incident. And follow that through, so that a scientific approach to risk-rating on an incident is obtained.
An incident risk categorisation should, after all, not be a judgement call from an analyst. It should be based on information on different artefacts, views of the CIA value, and all these different attributes.
Prioritisation
SecurityHQ’s algorithms calculate incident risk by considering the classification attributes, in accordance with VERIS, that contribute to the magnitude of the problem, such as the Kill Chain, Mitre ATT&CK, victim counts, asset criticality, and more. Analysts then apply predictive risk factors that increase or decrease the degree of risk. The output is a contextualised risk assessment for each incident. So that you know exactly what to tackle first!
How Does SecurityHQ Differ from Other Solutions?
No other company has a risk-based approach to incident classification. It does not exist.
SecurityHQ is the only organisation to use a scientific approach to risk classification around incidents. Our approach to data-driven document style of presentation is unique. And we are heavily leveraging the D3.js framework, this being a library for producing dynamic, interactive data visualisations.
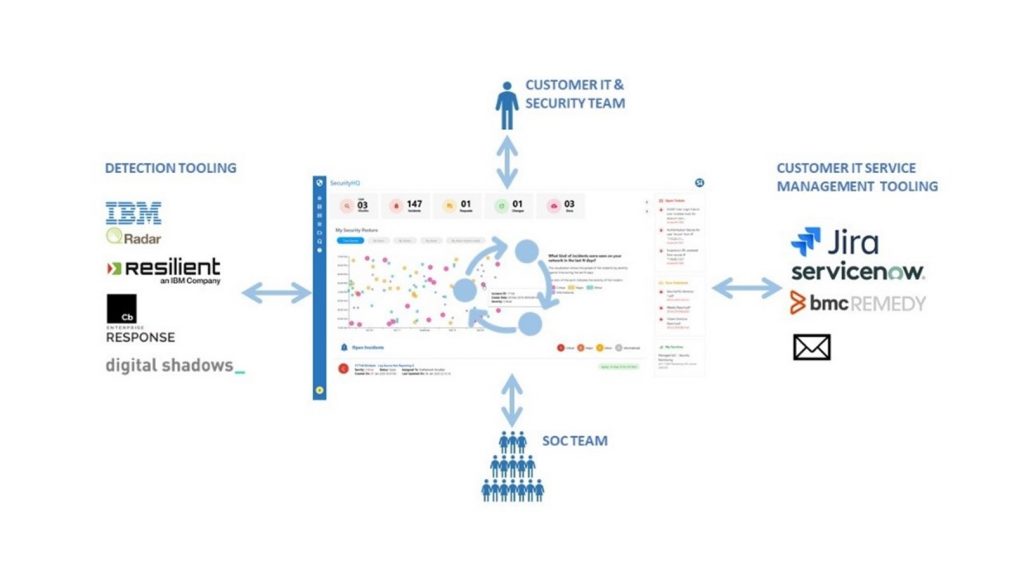
Interoperability
Our interoperability is also key. And our unified interface provides seamless access and collaboration via remote SOC’s. So that members can collaborate across IT and Security teams, to prioritise, remediate and rapidly respond to security risks. Escalate and action tasks to your ITSM tooling, including ServiceNow, Jira, and Remedy.
Actionable
SecurityHQ incorporates an ecosystem that allows us to build in playbooks, and permit some level of automation, particularly around containment responses. This means that, rather than just observe and notify, we can act on information, and say ‘alright, here is an issue, to fix it, let’s block that IP’.
Continual Development and Progression
Our roadmap for greater data visualisation
Seeing is believing. So, we want to be able to show data in a way that immediately articulates risk and threats, and to link data together to provide a clear picture that can be actioned against. In the end, IBM QRadar is an incredible SIM tool that we use. But its’s just an engine for us to carve data and to re-represent that data.
Our Incident Management platform covers all the services that SecurityHQ delivers. Regardless of whether it is MDR, EDR, Vulnerability Management, and so on, customers want to go to one place to see their security environment instantly.
Unified Platform
Have a question? Or, for more information regarding our new SecurityHQ platform, talk to one of our experts directly, here https://www.securityhq.com/contact/
“SecurityHQ’s success is largely down to our Incident Management & Analytics Platform. Security Operations demand collaboration across staff, department and third parties, armed with rich data and playbooks. SecurityHQ provides a unified security management platform to orchestrate incident response, prioritise actions, connect resources and visualise risk”. – Feras Tappuni, CEO
About SecurityHQ
Founded over 15 years ago, SecurityHQ prides itself on its global reputation as an advanced Managed Security Service Provider, delivering superior engineering-led solutions to over 120 clients, around the world.
By combining our dedicated security experts, cutting-edge technology and processes, customers receive an enterprise grade experience that ensures that all IT virtual assets, cloud, and traditional infrastructures, are protected.
Our mission is to provide world-class security operations to our clients and partners, to integrate processes seamlessly, and act as an extension of our user’s own teams. The result is a bespoke service that seeks to address the user’s specific risks and challenges and empowers their cyber safety.