Cyber Defense Center
Time-Based SQL Injection on Public Facing Website
Detection: SOC detected Time-Based SQL Injection on Public-Facing Website of a customer in financial services.
Description: The public-facing application was vulnerable to time-based SQL injection, allowing attackers to manipulate backend database queries. By introducing deliberate delays, attackers could confirm vulnerabilities and potentially extract sensitive data over time. No confirmed data exfiltration was observed during detection.
Attackers crafted malicious payloads (e.g., using conditional statements with delay functions such as PG_SLEEP) within input parameters to manipulate SQL queries.
Timely detection of the incident prevented exfiltration and potential impact on the website.
Recommendations: Adopt secure coding practices such as parameterized queries and strict input validation to prevent injection attacks. Enhance log monitoring with regex-based detection and deploy a WAF to block malicious payloads. Regular security testing and least privilege access to databases should be enforced.
Direct Send Email Abuse Resulting in Suspicious Sign-In and User Compromise
Detection: Use Case generated for risky sign-in from M365 defender which identified anomalous AiTM sign-in activity from an unusual geographic location shortly after the user received a suspicious email. Email logs confirmed the message bypassed traditional authentication checks using direct send methods.
Description: A user account was compromised following interaction with a malicious email delivered via a direct send configuration. This method allowed the attacker to send emails that appeared legitimate without passing through standard email authentication controls (e.g., SPF/DKIM/DMARC enforcement).
The user engaged with the email, leading to credential exposure. Shortly after, a suspicious sign-in was detected from an unrecognized location/device, indicating unauthorized access.
Recommendations: Restrict or disable direct send functionality and enforce strong email authentication mechanisms such as SPF, DKIM, and DMARC. Implement MFA and conditional access policies to reduce unauthorized access risks. Regular user awareness training and monitoring of anomalous sign-in activity are essential.
Threat Detection Engineering
New Detections for this Month
Linux: Shadow File Direct Modification Detected (P3)
This detection identifies suspicious attempts to directly modify the /etc/shadow file on Linux systems using command-line utilities such as sed, echo, tee, cp, or mv. The /etc/shadow file stores hashed passwords and is highly sensitive; direct manipulation is a strong indicator of unauthorized privilege escalation, credential tampering, or persistence mechanisms.
Security Impact:
- Detects unauthorized credential manipulation attempts
- Helps prevent privilege escalation and persistence via password changes
- Enhances visibility into critical system file tampering on Linux systems
Detection Name: Global: Audit and Compliance: Shadow File Direct Modification Detection.
Global Administrator Elevation to Azure Subscription Owner (P3)
Detect instances where a Global Administrator elevates their privileges to become an Azure Subscription Owner, which grants full control over all resources within the subscription. This action is highly sensitive and may indicate privilege escalation, misuse of administrative rights, or potential account compromise.
Security Impact:
- Full administrative control over Azure subscription
- Ability to:
- Modify or delete resources
- Grant permissions to other users
Detection Name: Global: Audit and Compliance: Global Administrator Elevation to Azure Subscription Owner
Threat Management
SecurityHQ’ s Threat Management Team manages various endpoint security, cloud security and network security solutions for customers. Following section highlights some key security insights.
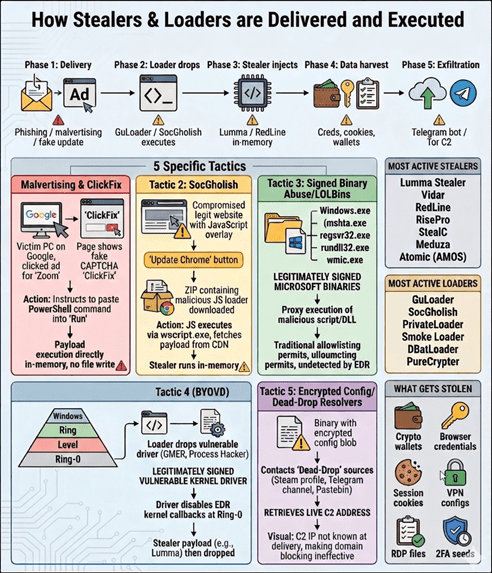
From ClickFix to Credentials Theft: Defeating the Latest Stealer & Loader Tactics
What is Stealer :
An information stealer is malware designed to silently harvest sensitive data from an infected endpoint browser-saved credentials, session cookies, crypto wallets, VPN configs, RDP files, and autofill data. It exfiltrates everything to an attacker-controlled server, typically within seconds of execution, then deletes itself. No persistence is required because the damage is done immediately.
What is a Loader :
A loader is malware whose sole purpose is to establish a foothold on a victim machine and silently fetch and execute a secondary payload a stealer, ransomware, RAT, or banking trojan. Loaders are intentionally lightweight and heavily obfuscated to bypass AV and EDR. They are typically the first stage in a multi-phase attack chain.
SecurityHQ Recommendations:
Method 1. Configure Attack Surface Reduction rules and credential protection in MDE
The following ASR policies directly target the delivery chains and execution techniques used by stealers and loaders including LOLBin abuse, script execution, and LSASS credential access.
security.microsoft.com → Settings → Endpoints → Attack surface reduction rules
| Policy / Setting | Status |
|---|---|
| Block execution of potentially obfuscated scripts | Block |
| Block Office apps from creating child processes | Block |
| Block Win32 API calls from Office macros | Block |
| Block process creations from PSExec and WMI | Block |
| Block credential stealing from Windows LSASS | Block |
| Block process creations from PSExec and WMI | Block |
| Block untrusted and unsigned processes from USB | Block |
| Block JavaScript or VBScript from launching downloaded executable content | Block |
Method 2. Enable Credentials Guard and LSASS protection
Enable the following MDE options from MDE and Intune for Credential Guard and LSASS protection.
| Policy / Setting | Status |
|---|---|
| Enable Credential Guard (via Intune device config) | Enable |
| LSASS process protection (PPL) | Enable |
| EDR in block mode | Enable |
| Network protection | Enable |
Configure CrowdStrike Falcon prevention policy and IOA rules for stealer and loader detection
Configure prevention policy – Credential theft and LOLBin protections
Falcon Console → Endpoint Security → Prevention Policies → [Custome Policy].
| Policy / Setting | Status |
|---|---|
| Suspicious script and command prevention | Block |
| Credential dumping prevention | Block |
| Enhanced DLL load visibility | Block |
| Suspicious process prevention | Block |
Threat Hunting
SecurityHQ’ s Threat Hunting team conducted hunts focused on general endpoint activities seen in the customer’s environment. Following section highlights hypothesis, hunts and top actions recommended to the customers.
Hypothesis:
An adversary may be operating on one or more endpoints by abusing legitimate system processes and native operating system functionality to establish persistence, perform internal reconnaissance, and exfiltrate data in a low-noise manner.
These activities are designed to evade traditional signature-based detections and can be identified through behavioral anomalies observed in process execution, registry modifications, service creation, and network telemetry collected via EDR.
Context:
This threat hunt focuses on detecting stealthy adversarial behavior that leverages trusted system binaries and native OS utilities (Living-off-the-Land techniques) to bypass conventional security controls.
Attackers increasingly avoid dropping obvious malware and instead rely on:
- Legitimate tools such as PowerShell, CMD, WMIC, and system services
- Execution from user-writable directories (e.g., AppData, Temp, Downloads)
- Native persistence mechanisms (registry keys, services)
- Low-frequency, high-evasion data exfiltration methods
Because these techniques blend with normal administrative activity, detection requires behavioral analysis and anomaly-based hunting rather than reliance on static signatures.
The investigation analyzes:
- Process execution patterns and command-line behavior
- Registry modifications associated with persistence
- Service installation activity
- Endpoint reconnaissance indicators
- Outbound network communication patterns
- Use of obfuscation in command execution
The goal is to identify early-stage compromise, persistence establishment, and potential data exfiltration while minimizing false positives through contextual filtering and baselining.
Threat Hunting Approaches:
1. Execution & Persistence Abuse Detection
Analyze execution of trusted system binaries (e.g., PowerShell, CMD, WMIC, svchost) from non-standard or user-writable paths, along with monitoring:
- Suspicious service creation
- Registry persistence (Run keys, Winlogon, IFEO, SilentProcessExit)
These behaviours indicate living-off-the-land abuse and persistence establishment.
2. Behavioral & Command Execution Analysis
Identify anomalous process behaviour such as:
- High-frequency reconnaissance commands (whoami, net user, nltest, ipconfig)
- Obfuscated or encoded command execution (-enc, iex, Base64)
- Unusual parent-child process relationships
These patterns help detect stealthy attacker activity and defense evasion techniques.
3. Network & Exfiltration Activity Monitoring
Monitor outbound network activity to detect:
- Connections to rare or unapproved file-sharing domains
- Non-browser processes initiating external communication
- Low-frequency or beacon-like traffic patterns
Correlate process and network telemetry to uncover data exfiltration and command-and-control activity.
Recommendations: Based on the observed threat landscape, the following actions are recommended:
- Enable Constrained Language Mode for non-admin users.
- Block Powershell executions from Non admin users or restrict executions for Encoded Commands and Invoke-Expressions
- Restrict script execution from user-writable directories like %AppData% %Temp% %Downloads% %Public% and apply tighter PowerShell policies for non-admin users.
- Eliminate or strictly restrict internet-exposed authentication services, especially SMB.
- Block non-Admin modification of Registry like HKCU\..\Run or HKLM\..\Run.
- Restrict Registry Storage of Network Configurations Registry values containing IP:Port patterns
- Block .ps1, .vbs, .js from email and web
- Enforce outbound filtering for non-browser processes
- Restrict communication towards filesharing cloud domains that are not approved by the organization.
Incident Response – Success Story
Time-Based SQL Injection Attempt
Overview
SecurityHQ SOC identified a Time-Based SQL Injection attempt targeting a public-facing web application belonging to a financial services customer. Immediate major incident management call was setup with key stakeholders and Incident response
The attack leveraged database delay functions to probe backend query execution behavior, indicating an attempt to validate input handling weaknesses and potentially extract sensitive data.
Early detection and response ensured that the activity was contained before any confirmed data exfiltration or service disruption occurred.
What Happened
During routine monitoring, the SOC detected anomalous web application requests containing crafted SQL payloads designed to manipulate backend database queries.
The attacker utilized time-based techniques, specifically injecting conditional logic combined with delay functions (e.g., PG_SLEEP), to observe response timing differences. This method allows attackers to infer database responses without directly retrieving data.
Key observations:
- Malicious payloads embedded within application input parameters
- Repeated requests introducing intentional delays to validate vulnerability
- Indicators consistent with blind SQL injection techniques
- No evidence of successful data extraction or lateral movement
The activity suggests that the attacker was in the reconnaissance and validation phase, attempting to confirm exploitability before proceeding to data extraction.
Threat Actor Attribution (Assessment):
At this stage, there is no direct attribution to a specific threat group.
However, the observed techniques align with Opportunistic attackers or automated scanning tools targeting publicly exposed applications
SecurityHQ IR team successfully responded to the incident thereby limiting the impact, and carried out necessary response actions including hardening of existing security controls to prevent future reocurrences.
Here are key Strategic Controls that can prevent similar incidents in your environment:
- Implement parameterized queries / prepared statements to eliminate SQL injection risks.
- Enforce strict input validation and sanitization across all user inputs.
- Conduct regular secure code reviews.
- Deploy regex-based detection rules to identify SQL injection patterns.
- Perform regular vulnerability assessments and penetration testing (VAPT).
Authors